The New Face of Account Takeover in Healthcare
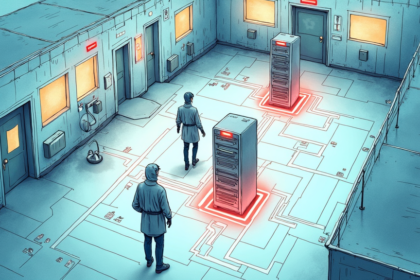
Scattered Spider, the cybercrime group known for high profile intrusions, is evolving its tactics to exploit identity processes and help desk workflows. Rather than relying solely on password theft, attackers now use a combination of automation, social engineering, and AI driven manipulation to bypass authentication. For healthcare organizations, this shift is particularly dangerous because hospital IT help desks often handle sensitive access requests for electronic health records (EHRs) and medication administration systems. When an attacker posing as a clinician calls the help desk to reset credentials, the consequences can extend beyond data theft to direct risks for patient safety.
Implications for Hospital Security Teams
Healthcare CISOs must recognize that traditional one time passcodes (OTPs) sent via SMS are no longer reliable. Fraudsters routinely intercept or socially engineer these codes to take over accounts that control clinical systems, billing portals, and telehealth platforms. The same techniques that drain bank accounts can now be used to access controlled substance logs or modify patient records. Hospitals should adopt continuous identity verification across the entire session, not just at login. This means layering behavioral analytics, device intelligence, and step up authentication for any action that affects ePHI, such as prescribing medications or updating allergy lists.
What This Means for Healthcare Organizations
For health systems, the stakes are uniquely high. A successful account takeover can lead to HIPAA breaches, disrupted clinical operations, and regulatory penalties. Attackers like Scattered Spider specifically target help desks because healthcare staff are trained to be helpful under pressure. Defenses must include rigorous caller verification protocols, mandatory multifactor authentication with phishing resistant methods, and real time monitoring of privilege escalation within EHR platforms. Compliance with the HIPAA Security Rule now requires addressing these evolving identity attack vectors as part of the required risk analysis. Healthcare organizations should treat every help desk call as a potential attack surface and invest in identity threat detection and response (ITDR) capabilities tailored to clinical workflows.
Source: Healthcareinfosecurity