The Strategic Value of Active Defense in Healthcare
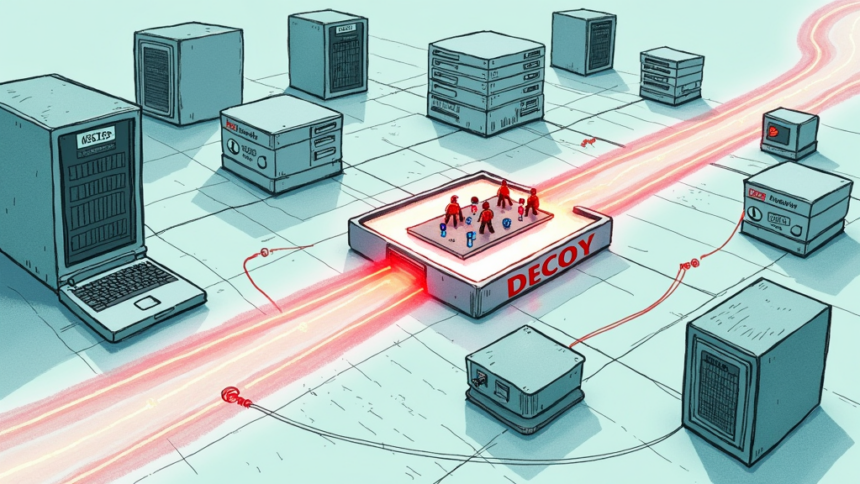
Healthcare organizations are prime targets for cyberattacks, yet many struggle to keep pace with the sheer volume of security alerts. Moving beyond a purely reactive stance, a growing number of health systems are adopting active defense strategies, including deception technology. By deploying decoys, honeypots, and lures such as fake patient records or simulated medical devices, security teams can misdirect attackers, detect intrusions early, and gather intelligence on adversary behavior without risking actual clinical systems. This approach allows a hospital SOC to shift from chasing noise to focusing on validated threats.
Integrating Deception with Modern Security Operations
Advanced deception platforms can now integrate with existing security tools like SIEMs and SOAR systems. When an attacker interacts with a decoy, the platform can trigger automated responses such as isolating a compromised workstation or alerting the incident response team. For healthcare organizations, this means faster containment of lateral movement before it reaches critical systems like EHR databases or medical imaging networks. This strategy also supports compliance with HIPAA and HITECH by providing detailed audit trails of unauthorized access attempts.
What This Means for Healthcare CISOs
For a hospital CISO, the value proposition is clear: deception technology reduces dwell time and improves threat detection accuracy. In a sector where uptime is directly tied to patient safety, any tool that reduces false positives while catching real threats sooner is critical. However, these systems must be carefully architected to avoid any risk of a decoy being confused with a real patient device. When properly implemented, deception provides a cost-effective force multiplier for understaffed healthcare security teams, allowing them to defend a complex attack surface with limited resources.
Source: Healthcareinfosecurity